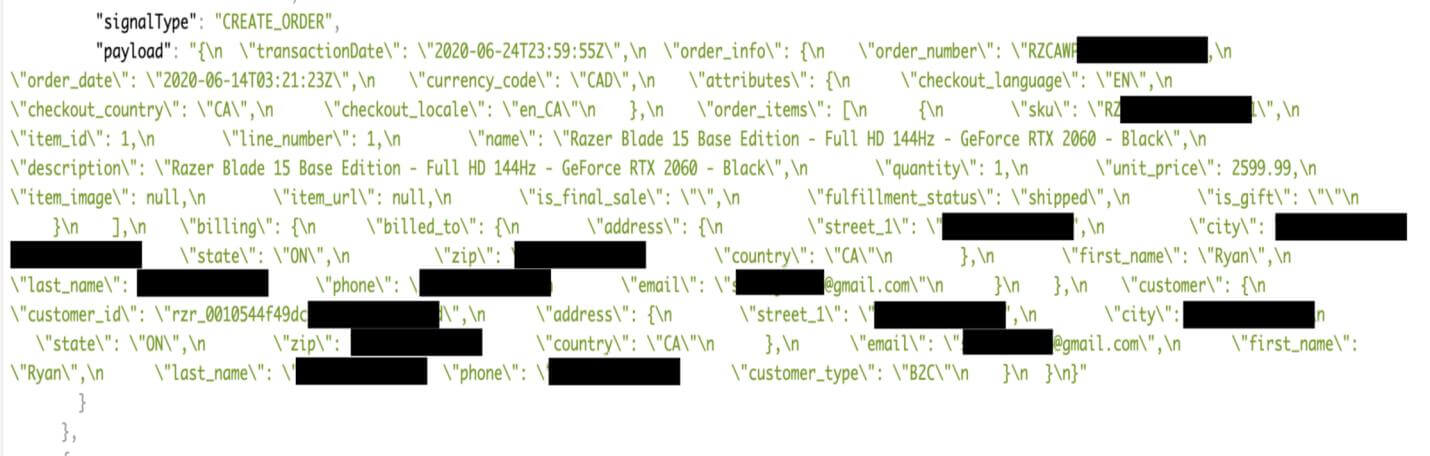
Gaming hardware firm RAZER has accidentally exposed over 100,000 customers’ personal data for close to a month, according to a report by a cybersecurity consultant, Volodymyr Bob Diachenko. He discovered a security breach over at hardware peripheral manufacturer Razer. Mr. Volodymyr found a badly configured Elasticsearch cluster filled with over 100,000 data entries of Razer customers.
The data was available for nearly a month for hackers to exploit. Customer data such as addresses and emails were made publicly available due to a server misconfiguration since Aug. 18, 2020; however, no credit card information or password was likely exposed.
“Based on the number of the emails exposed, I would estimate the total number of affected customers to be around 100K,” Diachenko wrote in his post. He added that he immediately reached out to the company regarding the exposure, but it took three weeks before he received a response from Razer.
As mentioned above, Razer’s website was made publicly available on August 18 because of a server misconfiguration. Leaked data included full name, email, phone number, customer internal ID, order number, order details, billing and shipping address. What appears to be more dangerous is that the Elasticsearch cluster was not only exposed online, it was also being indexed by a search engine, making the data more easily accessible via the Internet. This appears to be the website ADMIN’s fault, since there was no hacking required in doing this, and the front door was left open.
Diachenko also added in his post that the customer records could be used by criminals to launch targeted phishing attacks wherein the scammer poses as Razer or a related company. “Customers should be on the lookout for phishing attempts sent to their phone or email address. Malicious emails or messages might encourage victims to click on links to fake login pages or download malware onto their device,” he warned.
I must say I really enjoyed my conversations with different reps of @Razer support team via email for the last couple of week, but it did not bring us closer to securing the data breach in their systems. pic.twitter.com/Z6YZ5wvejl
— Bob Diachenko 🇺🇦 (@MayhemDayOne) September 1, 2020
Razer customers could be at risk of fraud and targeted phishing attacks perpetrated by criminals who might have accessed the data, Diachenko cautioned. Razer has confirmed the issue in an email to The Verge and said that customers that have any questions about the leak can reach out at this email address, DPO@razer.com.
Razer, known for its high-end gaming gear such as laptops and keyboards, has headquarters in both California, in the United States and Singapore. Upon discovering the leak, Mr Diachenko immediately notified Razer through its support channel. Razer said the error was fixed last Wednesday, prior to the lapse being made public.
In a statement, the company acknowledged the server misconfiguration.
“We were made aware by Volodymyr of a server misconfiguration that potentially exposed order details, customer and shipping information. No other sensitive data such as credit card numbers or passwords was exposed,” the company said. “The server misconfiguration has been fixed on September 9, prior to the lapse being made public. We would like to thank you, sincerely apologize for the lapse and have taken all necessary steps to fix the issue as well as conduct a thorough review of our IT security and systems. We remain committed to ensure the digital safety and security of all our customers.”
Thanks, Ars Technica.
Hello, my name is NICK Richardson. I’m an avid PC and tech fan since the good old days of RIVA TNT2, and 3DFX interactive “Voodoo” gaming cards. I love playing mostly First-person shooters, and I’m a die-hard fan of this FPS genre, since the good ‘old Doom and Wolfenstein days.
MUSIC has always been my passion/roots, but I started gaming “casually” when I was young on Nvidia’s GeForce3 series of cards. I’m by no means an avid or a hardcore gamer though, but I just love stuff related to the PC, Games, and technology in general. I’ve been involved with many indie Metal bands worldwide, and have helped them promote their albums in record labels. I’m a very broad-minded down to earth guy. MUSIC is my inner expression, and soul.
Contact: Email